Anonymous is a group of hacktivists which rose to prominence for their involvement in various political struggles, such as, helping WikiLeaks publish documents or advising protesters on surpassing government censorship in the Arab Spring protests.
After lying low for a while Anonymous has popped up in headlines again in relation to the death of George Floyd.
The group boasts a flat hierarchy. Having no official spokesperson or leader, operations and aims are widely discussed and agreed upon using online anonymous chats or forums. This goes as far as being called by The Economist "The 24-hour Athenian democracy". This means that while for the purpose of this post we will refer to Anonymous using the word group, this doesn't signify a cohesive entity with a clear roadmap, but a group of cells (or single actors) that operate under the same name, but that can have widely different, and sometimes opposing, aims.
Digital traffic jams?
One of the most prevalent forms of attack Anonymous uses is taking down a website. The attack on the Minneapolis PD website is a recent example of it. When this attack is performed on big institutions, it provides a lot of publicity and cracks the image of immunity these institutions may have. Nevertheless, it is a low skill attack that has no long lasting effects on the institutions attacked, as I'll explain now.
A Distributed Denial of Service (DDoS) attack, the usual cause of a website being taken down, uses a swarm of internet connected devices (computers, security cameras, fridges...) that have been infected with malware, to overload the website's servers. If you imagine the infected devices (AKA bots) as cars, they would be jamming the highway, preventing real traffic from getting to the destination. Kudos to Cloudflare for this helpful analogy, click the link if you want a deeper dive on DDoS attacks.
 Photo by Cloudflare
Photo by Cloudflare
While DDoS is very flashy it rarely takes down the site for more than a few hours. Moreover, due to the rise of CDNs, they have become less effective. CDNs have servers in many locations around the world that can store and serve your website. Therefore, when attacking a website, instead of overloading one server, the attacker will have to overload a hundred of them. Returning to our analogy, now imagine that our cars are spread around the world and can only be used to block the nearest highway, we will then need many more cars to succeed in our blockade.
Dripping data
Anonymous has also repeatedly leaked sensitive information. While information has at times been truthful, this time it seems they just packed up whatever they could find on the internet. The database containing personal data about police officers is probably just a compilation of old data breaches, as renowned researcher Troy Hunt explains. Also documents on Trump were from a court case voluntarily dismissed by the accuser.
While some groups of Anonymous may have noble intentions, its flat hierarchy makes it extremely vulnerable to hijacking by external actors that are interested in making use of the group's reputation. This is why we should take any information coming from the group with more than a pinch of salt.
Direct "digital" action
The demise of Anonymous does not mean in any way that 'hacktivism' has been defeated. In fact it may prove more necessary now than it has ever been. As governments get to grips with monitoring and censoring social media, using it as a platform to organise protests will become more and more difficult.
This is why privacy centric apps that help protesters organise are going to play a big role in the future of political struggle. Some examples of successful uses are HKmap.Live, an app that was used by Hong Kong protesters to track police vehicles, by crowdsourcing data from its users. It proved so effective that the chinese government forced Apple to remove it from its store. Another example was the Tsunami Democràtic app that was used to organise protests in Catalonia, after the jailing of politicians for organising a referendum. This app used a distributed network (one where there is no central authority that possesses all the data) to share each protester's area and availability to orchestrate flash protests. All without sharing none of the user's data.
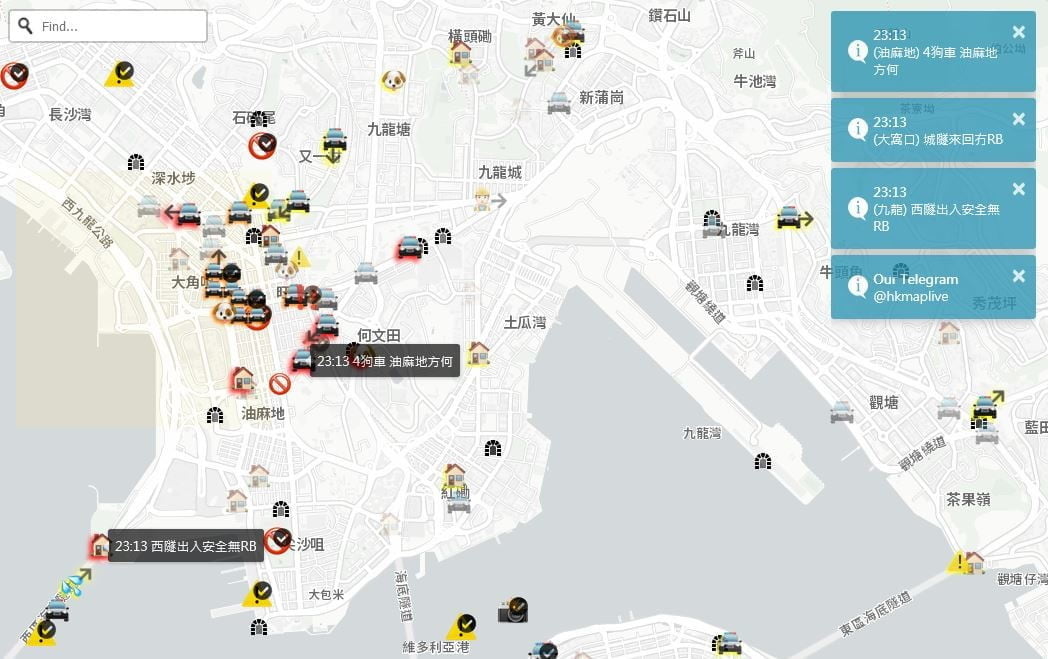 Photo by Digital Trends
Photo by Digital Trends
TLDR: Although traditional 'hacktivist' methods, like those used by Anonymous seem to be dying out, 'hacktivists' will need to play a crucial role in future protests to protect demonstrators from the surveillance state they are fighting.